thesyndrome How long have they known about this? Who was 'selectively targeted'? They need to provide more information, because 7 months is a REALLY LONG TIME to potentially have had a trojan on your device without knowing that a service you used might have been hijacked, and if they say the hackers had access to the server until December 2nd, then that means it's been at least 2 months that they have known about this breach and decided to only now tell people. Reply
DS426 frantyk said: Who was 'selectively' targeted, have they shared the code used for this logic. Would be nice to know if it was at least country specific, as I have updated n++ since aug last year! So far, it appears no individuals and organizations have been publicly named. Also, no IoC's according to their statement at Notepad++ *EDIT* however , Rapid7 provided details on artifacts, including IoC's, in their technical write-up of their investigation. https://www.rapid7.com/blog/post/tr-chrysalis-backdoor-dive-into-lotus-blossoms-toolkit/That said, if the attribution of the threat actor is correct, we know what the targeted geographies and sectors are (even as this incident probably wouldn't run the full gamut of Lotus Blossum's target scope). "Rapid7 Labs, together with the Rapid7 MDR team, has uncovered a sophisticated campaign attributed to the Chinese APT group Lotus Blossom. Active since 2009, the group is known for its targeted espionage campaigns primarily impacting organizations across Southeast Asia and more recently Central America, focusing on government, telecom, aviation, critical infrastructure, and media sectors." Specific to this Notepad++ incident, Kevin Beaumont, a well-known security researcher, also investigated the incident and said his victim(s) were in East Asia and were in financial services and telecom industries. Reply
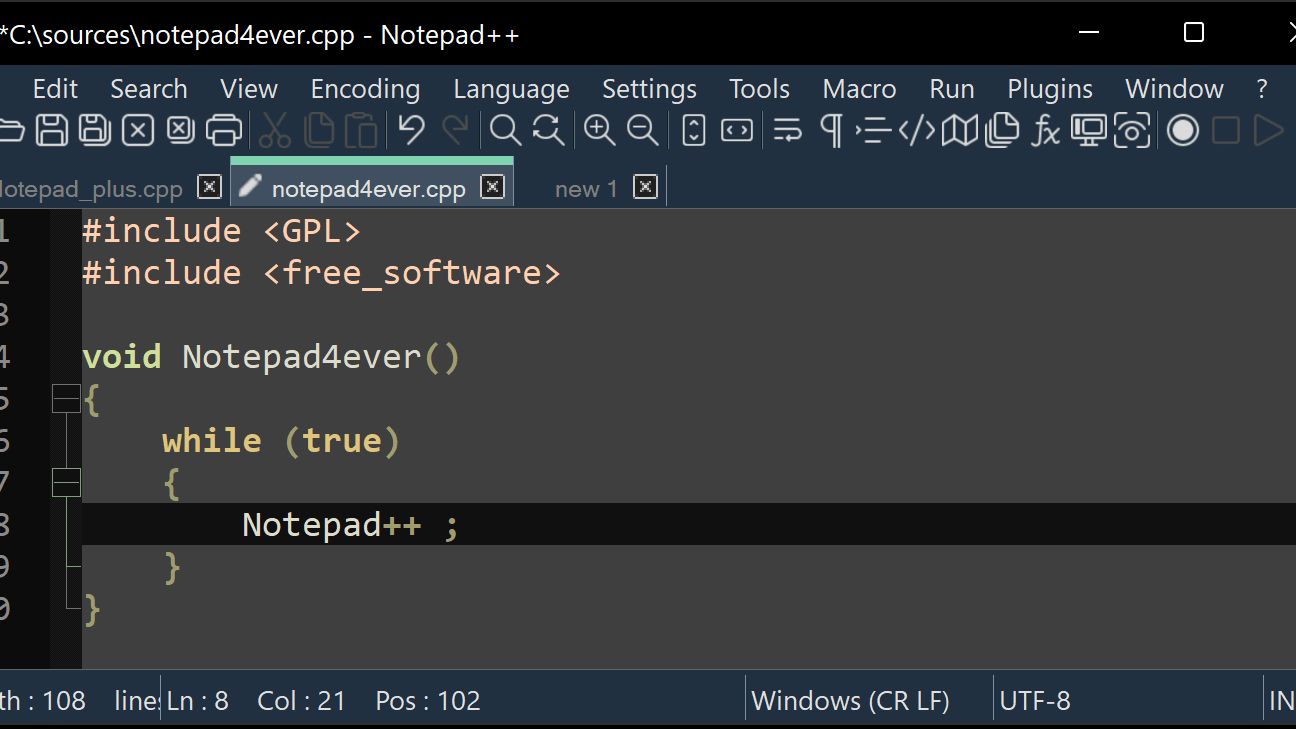
DS426 thesyndrome said: How long have they known about this? Who was 'selectively targeted'? They need to provide more information, because 7 months is a REALLY LONG TIME to potentially have had a trojan on your device without knowing that a service you used might have been hijacked, and if they say the hackers had access to the server until December 2nd, then that means it's been at least 2 months that they have known about this breach and decided to only now tell people. Read above for the "who". It appears to me that Notepad++ learned about it on December 9, 2025 as reported to them by security researchers. https://notepad-plus-plus.org/news/v889-released/ State-sponsored espionage attacks tend to have long dwell times, yes. It's no uncommon to find instances where these incidents went back over a year. Reply
Key considerations
- Investor positioning can change fast
- Volatility remains possible near catalysts
- Macro rates and liquidity can dominate flows
Reference reading
- https://www.tomshardware.com/tech-industry/cyber-security/SPONSORED_LINK_URL
- https://www.tomshardware.com/tech-industry/cyber-security/notepad-update-server-hijacked-in-targeted-attacks#main
- https://www.tomshardware.com
- From Pilot to Profit: Survey Reveals the Financial Services Industry Is Doubling Down on AI Investment and Open Source
- NVIDIA DRIVE AV Raises the Bar for Vehicle Safety as Mercedes-Benz CLA Earns Top Euro NCAP Award
- Save nearly 50% off on this thin-and-light laptop on Best Buy — Snapdragon X-powered Asus Vivobook 14 now on sale for just $379.99
- Fake Samsung 990 Pro passes basic checks but runs slower than a USB 2.0 drive — counterfeit SSDs proliferate as NAND shortage creates the perfect storm for bogu
- China-made Loongson 12-core chip is approximately three times slower than six-core Ryzen 5 9600X — 3B6000 hampered by low clock speeds in Linux benchmarks
Informational only. No financial advice. Do your own research.
