The story starts when Mendes decided to order the Ledger device from a "major marketplace" in China. He chose to do so because, being a non-Chinese citizen currently located in Shenzhen, importing one from abroad, directly from Ledger, "comes with its own headaches." The device's price was reportedly the same as that of a legitimate unit, but nevertheless, Mendes kept his suspicion mode engaged and installed Ledger's official software before the Nano S+ arrived.
True to the unfortunately expected form, after the device arrived, Mendes noticed it was "clearly" a counterfeit, a fact verified by the Ledger software, which marked it as non-genuine. True to his profession, Mendes decided to tear apart the device instead of tossing it, and found quite an elaborate scheme at work — one that's likely catching other unsuspecting users off guard.
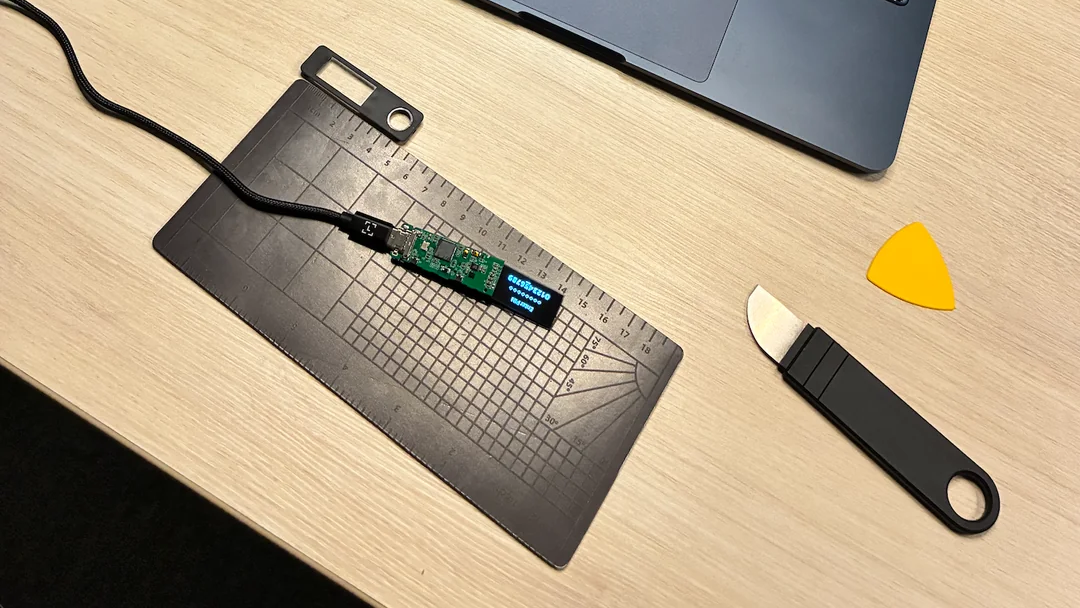
You may like Exceptional fake SSD clone of Samsung 990 Pro is almost impossible to spot Fake Samsung 990 Pro passes basic checks but runs slower than a USB 2.0 drive Fake Samsung 990 Pro SSD pops up in Europe, has a blue PCB and doesn't even work After prying open the case, Mendes found that all chip markings had been scraped off, but eventually managed to identify the central unit as an ESP32-S3 system-on-a-chip (SoC). The device spoofed its identification, claiming it was a "Nano S+ 7704" from Ledger's factory, complete with a serial number. After inspecting the firmware, Mendes quickly found his test PIN and seed phrases for two wallets, as well as hard-coded credentials to reach C2 (command-and-control) servers that slurped up the data.
The presence of Wi-Fi and Bluetooth antennas initially led Mendes to believe the data would be exfiltrated via those methods when on public Wi-Fi, or perhaps via a USB keylogger. Instead, he found that it's actually a fake Ledger app that does the data harvesting. Unaware users will be led to a page that looks like a clone of ledger.com, from which they can download malicious Android, Windows, or macOS apps.
He took apart the app, and sure enough, it was signed with an Android Debug certificate, tracks the device's location even after being closed, and sends data to the C2 servers. The download link QR code, presumably on the package or paper instructions, was likewise tainted. Adding insult to injury, the firmware monitors account balances via their public keys, presumably letting the thieves hear a "ka-ching!" sound whenever funds are deposited.
The expert thinks this device is sold to first-time cryptocurrency users looking for the added security of a hardware wallet, and it's not hard to imagine it working well for that purpose. Even a sleep-deprived professional might use the download link on the box instead of going straight to ledger.com.
Get Tom's Hardware's best news and in-depth reviews, straight to your inbox.
Key considerations
- Investor positioning can change fast
- Volatility remains possible near catalysts
- Macro rates and liquidity can dominate flows
Reference reading
- https://www.tomshardware.com/tech-industry/cyber-security/SPONSORED_LINK_URL
- https://www.tomshardware.com/tech-industry/cyber-security/techie-buys-fake-ledger-nano-s-hardware-crypto-wallet-and-almost-falls-for-phishing-a-convincing-clone-would-have-caught-newbies-unaware#main
- https://www.tomshardware.com
- Efficiency at Scale: NVIDIA, Energy Leaders Accelerating Power‑Flexible AI Factories to Fortify the Grid
- From RTX to Spark: NVIDIA Accelerates Gemma 4 for Local Agentic AI
- Crazed World of Warcraft gamer plays game with 3D-printed hot dog controller — the left wiener quad-array controls movement, the right triggers abilities
- New Adobe Premiere Color Grading Mode Accelerated on NVIDIA GPUs
- Nvidia CEO Jensen Huang ‘nearly lost his composure’ when pressed on selling chips to China — ‘You’re not talking to someone who woke up a loser’
Informational only. No financial advice. Do your own research.
